Why do we need phishing training in 2023?
Lately I have seen this topic floating around Twitter and Linkedin, and almost every time I disagree with what I’m reading. The popular opinion right now – at least within my sphere of technical security professionals – is that phishing training is not (any longer?) needed and we should get rid of it.
The reasoning seems to be one or more of the following:
- Phishing training is only there to shame users, not to actually help
- We should have technical controls to prevent all steps of this
- The internet is meant to be clicked on, let users click and open all attachments!
- Phishing training is lame, tech is awesome

IT-Security should be deployed in depth
Personally I have never really understood this whole black and white perspective, even less so when it comes to security. I strongly believe that a layered approach (“defense in depth”, “layered security approach”, “the onion approach”) is the way forward instead of simply relying on a single point of defense.
Perhaps that security aware user who didn’t open the attachment is what stops your organization from initial (or complete) compromise.
It’s very easy to simply say “we should just have technical controls which catches all emails with malicous intent, blocks the urls, and MFA to stop unwanted logins”. And well yes in an ideal world that would have been nice scenario, unfortunately that’s now what the real world looks like. Some malicious emails will make it through the filtering, some users will click on that phishing link, some users will enter their credentials, and some users will approve the MFA prompt from an attacker.
Let’s have technical controls in place to try and mitigare as much as we possibly can, but for those last percentages that are missed. Perhaps that security aware user who didn’t open the attachment is what stops your organization from initial (or complete) compromise.
The whole reasoning of “Some users will still fall for phishing emails even after phishing training, therefore we don’t need phishing training” makes no sense.
Let’s play with the idea that you have this 100% perfect email filtering setup which literally stops all malicious emails and you wholeheartedly rely on this. Then your user signs in to their their personal gmail/hotmail/other random email service which doesn’t have that 100% perfect security that you relied on and now all that is bypassed. Or vice versa, you rely too heavily on your EDR and on-prem/vpn solutions, which works great until your user signs in to your work O365/gmail from their home computer which has none of that.
The whole reasoning of “Some users will still fall for phishing emails even after phishing training, therefore we don’t need phishing training” makes no sense. It’s like saying that beacuse some malware might evade an EDR so therefore we don’t need an EDR, or that a penetration test will not find 100% of the vulnerabilities therefore we shouldn’t get one. It’s not about getting a perfect result from a single item, but having enough layers of security that it should get caught somewhere down the layers, that the success rate of an attack decreases for every layer it goes through. At the very least it should slow the attacker down to buy the blue team more time.
I don’t buy the “Internet is made to be clicked on, let users click and open attachments!”
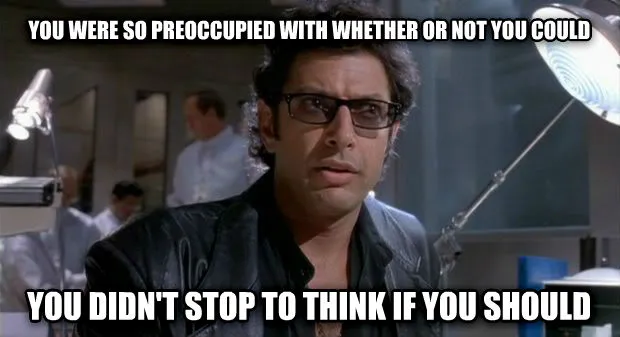
Well cars usually have quite a big engine and are made to go way faster than the speed limit allows. That doesn’t mean you can – or should – drive recklessly and fast just because they were made for it. You also need to attend some education first, to know what you can and cannot do, you learn about speed limits, you learn to brake effectively and so on. My point is, just because you can do something doesn’t mean you should. Did you learn nothing from Jurassic Park?!
Phishing Training might come with added benefits
Another added benefit of this is that it raises the security awareness amongst your users. It might be applied when your user receives a phishing email on their personal email, opened on the home device of some sort. Maybe they will be approached physically but someone and thanks to their security training they spot this as something unusual and might not fall for it. If we can raise security awareness not only in the more technical departments but also in HR, Finance, Maintenance, the reception etc, then we’ve come a really long way.
No, let’s continue having phishing training as a way of improving our security. Just make sure you choose a good vendor and that your intent is to educate and help your users and not to play the blame game. Communication is key






